DIGITAL LIFE

AirSnitch attack shows hackers can easily intercept encrypted Wi‑Fi traffic
AirSnitch is a newly-revealed attack on Wi-Fi networks that work across all major router brands and firmwares, including DD-WRT and OpenWrt. In an alarming turn for cybersecurity, researchers revealed a form of Wi-Fi attack that can entirely bypass client isolation on Wi-Fi, which is typically the only thing preventing attackers from intercepting data sent from your router to your device. There are caveats we'll discuss, but the sheer applicability of the attack across Wi-Fi providers is staggering, and makes the prospect of relying on public or shared Wi-Fi access points truly nightmarish, particularly for any sensitive data you may be handling on those networks. That warning doesn't just apply for coffee shops or other common access points—schools and universities and even some enterprise networks could be compromised by AirSnitch attacks.
Lead author of the related research paper (AirSnitch: Demystifying and Breaking Client Isolation in Wi-Fi Networks) Xin'an Zhou stated in an interview with Ars Technica that "AirSnitch breaks worldwide Wi-Fi encryption and it might have the potential to enable advanced attacks. Advanced attacks can build on our primitives to [perform] cookie stealing, DNS and cache poisoning. Our research physically wiretaps the wire altogether so these sophisticated attacks will work. It's really a threat to worldwide network security." He elaborated later that while some router manufacturers have already released mitigation updates and that more are expected to come, a few manufacturers have stated that "some weaknesses can only be addressed through changes in the underlying chips they buy from silicon makers." The lack of standardization in client isolation methods across manufacturers also throws a wrench into defending against AirSnitch, since solutions may end up being vendor-specific.
It's not all doom and gloom, thankfully. Co-author of the research paper Mathy Vanhoef also stated that AirSnitch is better described as an encryption bypass "in the sense that we can bypass client isolation. We don't break Wi-Fi authentication or encryption. Crypto is often bypassed instead of broken, and we bypass it. People who don't rely on client or network isolation are safe."
That last bit is the most important piece of information for most readers despite not being stated in the original paper and only mentioned after the Ars Technica piece's initial publication. Are you running a Wi-Fi access point with a dedicated Guest network? If so, it's essential that separate SSIDs are on separate VLANs if you want to protect your network from these attacks. If such options aren't available to you, you may be vulnerable until appropriate firmware patches are released or new router releases fix the underlying isolation vulnerabilities entirely.
A number of enterprise networks already separate SSIDs into their own VLANs, so the vulnerability there is less severe. But for networks with less-secured Guest access, especially public Wi-Fi networks, the danger is greatly increased. It's particularly problematic for those who use ISP-provided routers from providers like Comcast, whose Xfinity routers double as Guest access points for other Xfinity customers within range. As always, a fully-private network access point is best to protect yourself from attackers—though other, more commonplace attacks like "evil twin" attacks are still a concern.
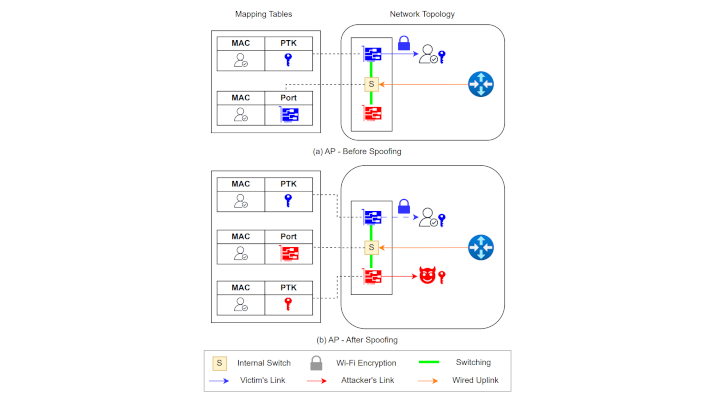
AirSnitch bypasses the so-called "client isolation," a feature offered by router manufacturers to prevent devices connected to the same access point from communicating directly with each other. The method works even when encryption is enabled.
This opens the possibility of a bidirectional "man-in-the-middle" attack, in which the attacker can intercept and modify the victim's traffic. In practice, this can enable the theft of cookies, passwords, and credit card data, as well as DNS poisoning.
In tests, 11 devices from manufacturers such as Netgear, D-Link, TP-Link, ASUS, Ubiquiti, and Cisco showed vulnerability to at least one variation of AirSnitch. Some of the flaws can be mitigated through firmware updates, but some manufacturers reported that certain vulnerabilities can only be corrected by modifying the hardware of the chips used.
Despite its severity, AirSnitch requires the attacker to already have some type of access to the Wi-Fi network or associated infrastructure, which raises the practical barrier to exploitation.
Tested models(below):
Tenda RX2 Pro
D-LINK DIR-3040
TP-LINK Archer AXE75
ASUS RT-AX57
DD-WRT v3.0-r44715
OpenWrt 24.10
Ubiquiti AmpliFi Alien Router
Ubiquiti AmpliFi HD Router
LANCOM LX-6500
by mundophone
No comments:
Post a Comment